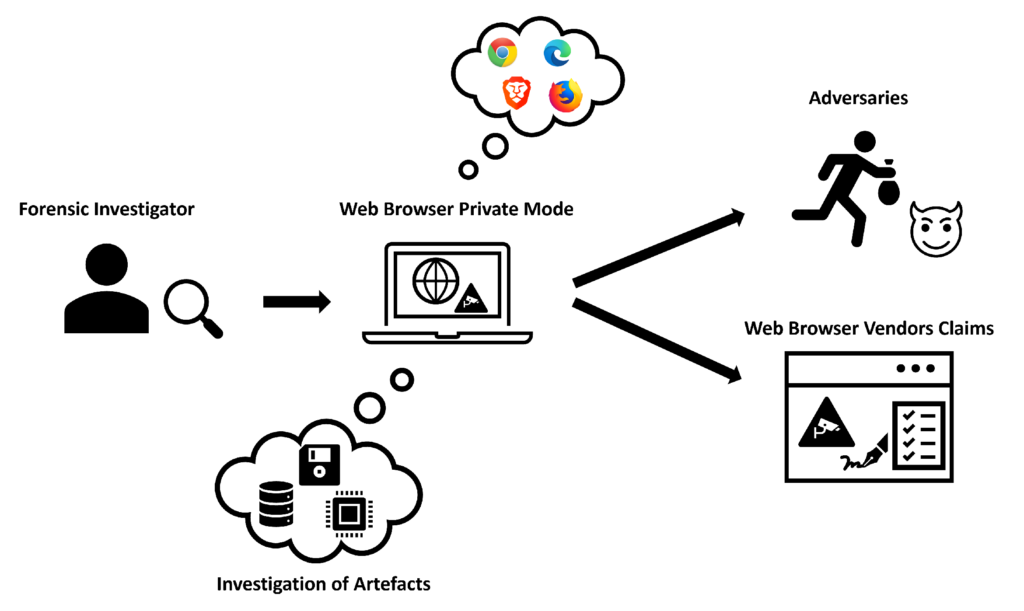
In the information technology era, where internet privacy and security are the norm, most internet users rely on tools like private browsing and Virtual Private Assessing the Security of Private Browsing Networks (VPNs) to protect their data and remain anonymous online.
Nonetheless, these technologies offer extra protection Assessing the Security of Private Browsing against assaults; however, it is critical to understand their security features and implications for your online security. In this article, we will look at the security of the feature in private browsing and VPNs, as described by our VPN experts, to determine whether they are safe enough for your online habits.
Understanding private browsing Assessing the Security of Private Browsing
Private browsing, often known as incognito mode or privacy mode in web browsers, allows users to access the web without saving browsing history, cookies, or other tracking Assessing the Security of Private Browsing data. Private browsing allows you to hide your browsing history from others who use the same device as you. However, private surfing does not provide perfect anonymity and protection from tracking by websites, ISPs, or tracking corporations.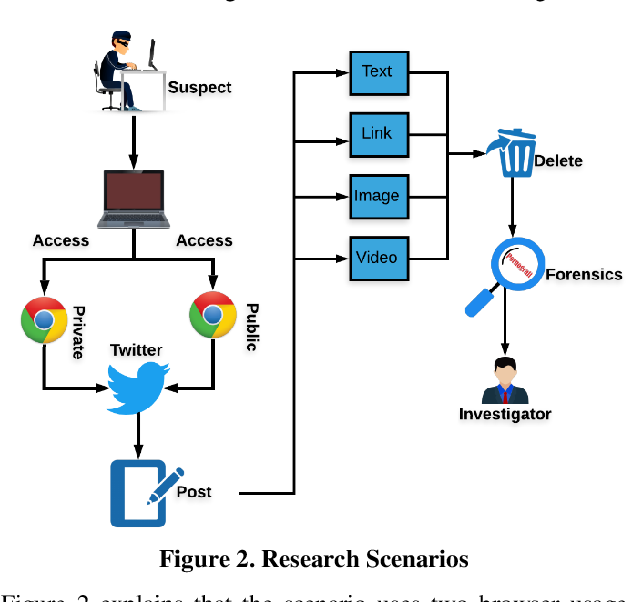
Evaluated the security of private browsing.
When discussing the security of private browsing, we must be aware of its limitations. Private browsing mode can keep your device private, but it cannot protect you from being tracked by those who have access to it, being monitored, or being attacked by hackers.
We spoke with a team of VPN professionals to get their thoughts on the security of private browsing. They believe that private browsing is an excellent technique Assessing the Security of Private Browsing to prevent your browser history from being saved on your device, but it does not encrypt your web activity or protect your information from being stolen by hackers or other third parties.
Understanding Virtual Private Network (VPN)
While VPNs give a larger answer to online privacy and security, they also provide a more comprehensive level of protection. A VPN creates an encrypted tunnel between Assessing the Security of Private Browsing your computer and a server provided by the VPN provider. VPNs employ an encryption tunnel to route your internet traffic, disguise your IP address, encrypt your data, and prevent websites from tracking your online activities.
VPN security is measured.
When considering the security of a VPN, numerous Assessing the Security of Private Browsing factors Assessing the Security of Private Browsing must be considered. These include encryption strength, provider logging policy, jurisdiction, kill switch feature, and DNS leak protection.
We asked our VPN expert team for their thoughts on the security of VPN connections. As some of them suggest, VPNs are very effective at protecting customers’ online privacy and security, but not all VPN service providers are equal. To ensure complete privacy of your online activity, choose a trusted VPN provider that offers strong encryption, a strict no-log policy, and advanced security features.
Choosing the right VPN
When considering the security of a VPN, numerous factors must be considered. These include encryption strength, provider logging policy, jurisdiction, kill switch feature, and DNS leak protection.
We asked our VPN expert team for their thoughts on the security of VPN connections. As some of them suggest, VPNs are very effective at protecting customers’ online privacy and security, but not all VPN service providers are equal. To ensure complete privacy of your online activity, choose a trusted VPN provider that offers strong encryption, a strict no-log policy, and advanced security features.
When selecting a VPN, it is critical Assessing the Security of Private Browsing to conduct research and choose a service that prioritizes security and user privacy. Choose a secure VPN that includes military-grade encryption, a no-logs policy, and additional security features like a kill switch and DNS leak protection.
In addition, compare the server locations, connectivity Assessing the Security of Private Browsing speeds, and gadget compatibility to your devices and operating system. Using reviews and suggestions from reputable sources, including our VPN specialists, is a wonderful approach to gather critical information for making the right selection when purchasing a VPN for security and privacy.
Conclusion: Balancing Privacy and Security.
Still, it’s worth noting that both private browsing and VPNs include Assessing the Security of Private Browsing security features designed to protect your data and ensure your online privacy. Nonetheless, they include gaps. Using incognito mode prevents your activity from being saved on the device, but it does not provide complete security against being observed or watched on the internet.
Tunnel technologies, such as PPTP and L2TP, work differently than VPNs by encrypting your web traffic and masking your IP address. You will achieve greater privacy and security while surfing the internet if you use a reputable VPN provider and the best internet privacy precautions. Finally, privacy and security in trade-offs should be analyzed and implemented using the appropriate tools and procedures according to your privacy requirements and preferences.
Furthermore, we cannot exaggerate the critical role of Managed Service Providers (MSPs) in cybersecurity. MSPs provide specific skills and services that can improve the overall security posture of both individuals and companies. MSPs play an important role in protecting against cyber attacks by installing strong security measures and offering proactive threat detection and incident response. Partnering with an MSP provides users with specialized security solutions and ongoing support, ensuring that their online activities are safeguarded against evolving threats and vulnerabilities.